Types of Web Application Security Testing

Web application security testing is a vital part of web development as there are many types of web app vulnerabilities that can be exploited by hackers. In this article, we’ll go over types of web application security testing and provide tips for web application security testing so you know how to keep your data safe from those pesky hackers.
What are the Types of Web Application Security Testing?
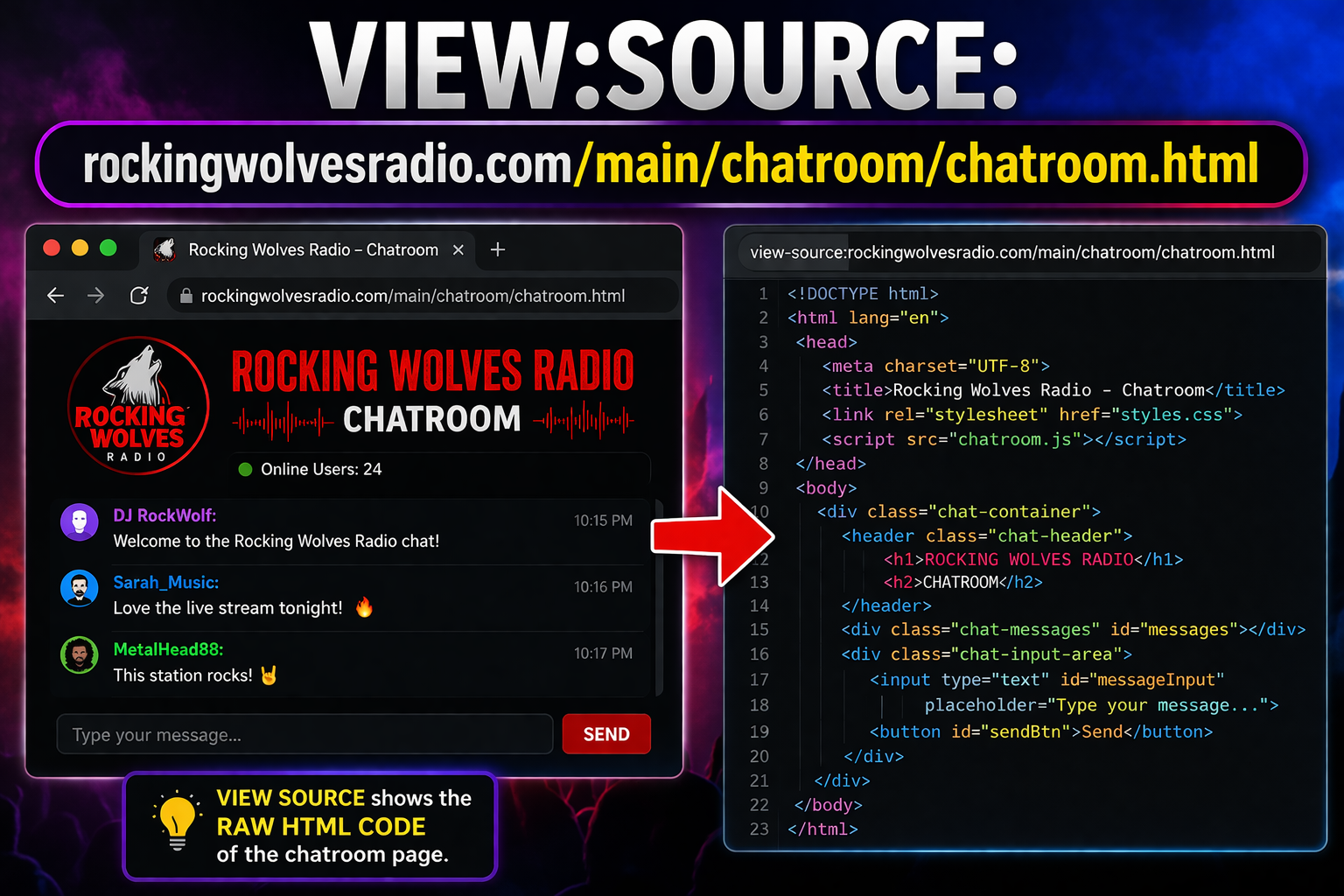
1. Dynamic application security testing (DAST) – Web application security testing that involves the use of real web browsers to test web applications. It is considered one of the best web app vulnerability scanning techniques because it tests how web apps respond when users interact with them in different ways, which can uncover many types of vulnerabilities like SQL injection and cross-site scripting (XSS).
2. Static application security testing (SAST) – Also known as source code analysis or white box penetration testing, SAST identifies software bugs or coding errors made by developers while they are creating a program. These flaws create opportunities for an attacker to exploit a system through its weakest point so they may be particularly dangerous if your site contains sensitive information about customers such as credit card numbers. A good example would be Heart bleed which was a result of SAST testing.
3. Manual web application security tests – Manual web app security tests are carried out by humans rather than automated tools so they can be more comprehensive, but they typically take longer to perform and are therefore less scalable. It is highly recommended that you have some form of web application vulnerability scanning in place as well because it will help speed up the process.
4. Application penetration testing – Web application penetration testing is different from web app security testing because it focuses on attacking the software to see how deep an intruder can get before they are detected. Such tests may be carried out by automated web vulnerability scanners or individual pen testers from reputed penetration testing companies, but you need to make sure that anyone who performs web application penetration testing for you has experience in this field as novice hackers could end up causing more damage than good.
Tips for Web Application Security Testing
1. Consider using a white-box approach – SAST and DAST both use a black-box approach which means that vulnerabilities are identified based on information submitted through input boxes like forms without knowing what’s going on inside of the code. This allows attackers to potentially bypass any protection methods implemented by developers such as firewalls and web application firewalls (WAFs). White box testing, on the other hand, is performed by those who know exactly what code they’re looking at so it can be much more effective.
2. Focus on automation – Automated web security testing gets better results than manual web app security tests because there’s less room for human error or bias and scanning tools typically run faster as well. However, make sure to combine your web vulnerability scanner with a proxy tool like OWASP Zap if you use one as this will allow you to easily switch between active scan modes without having to change any settings which could slow down the process.
3. Choose an automated web security testing solution that supports mobile apps – The number of mobile device users has been growing exponentially over the past several years and web apps are becoming more integrated into our lives. Web security scanners that don’t support web application testing for mobiles may miss out on vulnerabilities that could be exploited by hackers to steal sensitive data or damage your brand’s reputation through phishing campaigns.
4. Consider using manual web app security tests – Automated web vulnerability scanning tools can only see what they’re programmed to look for which means some flaws will go undetected unless you know exactly where to look, so it is recommended that you run at least one web penetration test every year regardless of how many automated scans have been completed recently. Manual web application security testing also tends to lead down different code paths than automatic scanners do because the tester has their own unique way of navigating web apps, so this can highlight vulnerabilities that automated web security testing software will miss.
5. Make sure your web app security team is up to date with the latest web application threats – The information provided in a web vulnerability scanner’s results should be taken into account by web application security testers when they write their own reports because it provides valuable insight regarding how attackers may try and hack your site which may help you discover new issues otherwise overlooked. If you’re not using any tools for pen-testing I highly recommend OWASP Zed Attack Proxy (ZAP) as an addition to whatever other solutions are used on the team. It’s free & open source, has great support available through IRC, Stack Overflow, etc., and offers plugins like Burp to help web app pentesters transition from a black box to a white-box testing approach.
Conclusion
The time to think about security is before you build the application. Once it’s built, it becomes exponentially more difficult and expensive to secure your website or app from hackers . Web Application Security testing should be one of the first steps in developing a new website or mobile app because if done correctly, this can prevent costly risks that could ruin your company’s reputation overnight. Good web application security means protecting against both technical vulnerabilities (e.g., SQL injection) as well as user-generated content such as spam messages, phishing attacks, etc.).