4 Principles of Sustainable Cybersecurity 2024

We have seen an alarming increase in cybersecurity threats and breaches worldwide in the last few years.
Every country in the world has been affected by different cybersecurity breaches. It’s no secret that the cybersecurity industry is developing at an instantaneous pace.
During the first half of 2021, Australian cybersecurity agencies recorded 446 cybersecurity breaches, which is already 16% more than the recorded events from the second half of 2020. Nevertheless, these breaches can be easily avoided using a good free cybersecurity tool such as a Virtual Private Network (VPN).
However, right now, what the world needs most is sustainable cybersecurity. Confused? Don’t worry. In this article, we will explain it to you in detail along with its four pillars.
What is Sustainable Cybersecurity?
When we talk about sustainability, we refer to a resource that doesn’t lose its existence regardless of how, when, and in what manner it is used. The same logic applies to sustainable cybersecurity.
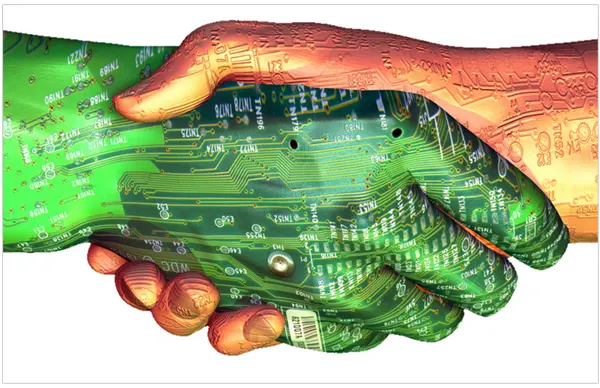
Cybersecurity is sustainable when it doesn’t lose its security level or get exhausted over time. That doesn’t matter how the security resource is being used or managed. It won’t be finished or affected by anything the company or business experiences.
Four Principles of Sustainable Cybersecurity
Sustainable cybersecurity has four pillars of working, popularly known as RAAR Principles. Here, we are going to discuss them in detail:
Reliability
While our technology is getting more advanced, it is also getting more complex. The same advancement provides technological advantages and creates room for error and risk.
A system that can tolerate faults can not truly exist without aligning with the security system. For example, if the security integrity is compromised, it will influence the whole process, and it is the same the other way around.
Reliability and security need to work together, and they depend on one another. It is a common mistake that many businesses make by thinking that if they handle the reliability, the security will be maintained or vice versa. This is the wrong approach.
If a system fails, we can say that it occurred due to the low reliability of hardware/software, defective security, or both.
While creating a new system, security and reliability should be an essential part of the strategy and execution. They need to exist and work together.
Accuracy
The quality of the security will be greatly affected if the security information isn’t accurate. The data has to be understandable by procedures and users simultaneously.
To protect certain assets, you need clear and accurate information about them. For example, you need to know about the on-site, third-party-owned assets, software, network systems, locations, and much more.
The more accurate information you have about everything, you’ll be able to secure them more effectively and efficiently.
Architecture
The main objective of security architecture is to guarantee that all the essential, mandatory, and necessary defenses against any cyberattack are integrated with security protocols, policies, business strategies, and other requirements.
It is also responsible for any modifications and upsets in the network and security. Architecture is the most crucial component of cybersecurity as it brings together user, procedure, and technology with the other three principal components.
Good architecture must guarantee that it contemplates threat modeling to evaluate threats and disclosed attack surfaces.
For example, if you are planning to add software or process to the system, then you should think about the following:
- What will data be processed by the application/process?
- How will the data be recorded and protected?
- The data will be accessed by whom?
- How will that data be accessed, and why?
Cybersecurity architecture will require regular assessment and updates. This will ensure that the cybersecurity services are generating the desired results.
Resiliency
The ability to acclimate and be equipped for varying circumstances to abide by possible disturbances and recuperate from them. Attaining resiliency in cybersecurity is not a new idea.

Acquiring a more elevated level of resiliency occurs over time; it’s a lengthy procedure. Implementing and sustaining a baseline security level is the first step on the journey of being resilient. It is then followed up by:
- Enforcing a robust security configuration management procedure.
- Increasing the standard of identification and access procedure.
- Having tough vulnerability management capabilities.
- Prioritizing hazards and fixing them.
You can not obtain resilience without having redundancy. They both are connected. Redundancy allows various assets, resources, and systems with similar functionality.
Final Thoughts
These four principles are not the only way of achieving sustainable cybersecurity. There are also various other ways to obtain it. But, by applying the principles mentioned above, you can at least continue to maintain the level of cybersecurity that we need to sustain attacks.
RAAR strategy also helps in making the Environmental, Social, and Governance (ESG) best practices, a priority. It is making everyone socially aware, addressing issues on the protection of business and employee data, and assisting in regulatory compliance, such as CCPA and the GDPR.
FAQs
What are the 5 basic principles of cybersecurity?
5 basic principles of cybersecurity are confidentiality, integrity, availability, authenticity, and non-repudiation of user data.
What are the 5 C’s of cybersecurity?
The 5 C’s of cybersecurity are change, continuity, cost, compliance, and coverage.
What are the three major types of cybersecurity?
Three major types of cybersecurity include network security, cloud security, and physical security.