Online Data Protection: 6 Tips for Better IT Security
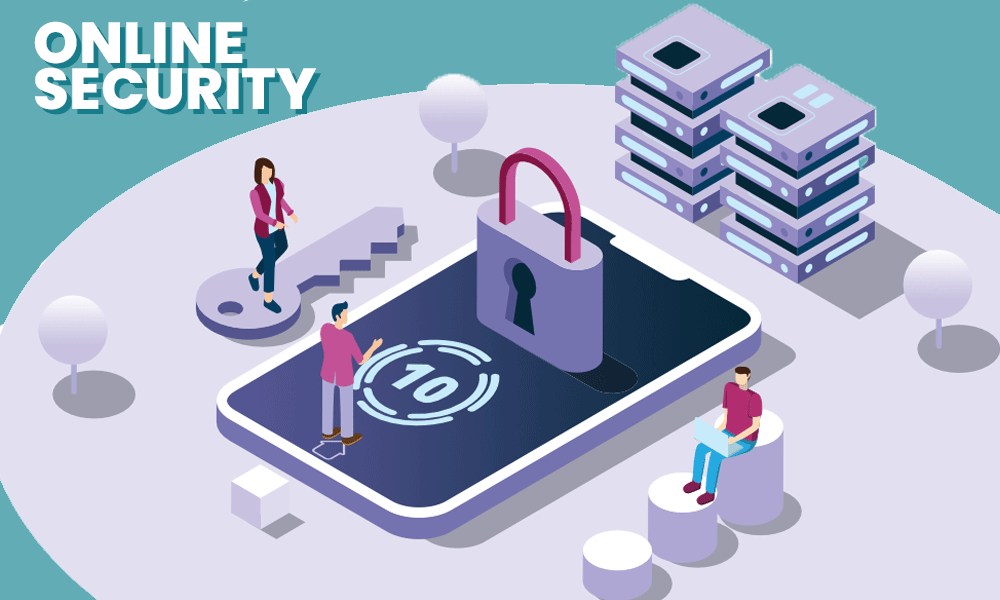
Undoubtedly, the internet has become a powerful means of information exchange. Most individuals and businesses use the internet for transactions and deals. Many share their personal information online through emails too. This digitalization, however, has increased the risk of cybercriminals attacking and stealing information online.
Businesses, irrespective of size, are loaded with exploitable information that makes them a perfect target for cybercriminals. Yet, many companies tend to neglect security concerns resulting in millions of dollars being flushed down annually. Surprisingly, 43% of all cyberattacks are targeted at small and medium businesses; it highlights the urgent need to start protecting your business’s data online.
To ensure that your online data is safe and to prevent data loss, you must take precautionary measures to secure the IT system. Here are six tips you can follow to make your company’s data safe:
Hire Cybersecurity Professionals
Improving security can be a long and detailed process; you might have to hire several professionals for short-term and long-term projects. A Cyber Risk and Compliance Specialist can identify the risks to your current system. Then, cyber engineers can help mend your existing system and develop a robust setup. Before your system is ready to be used, one last step is confirming the system is safe enough. You must hire a professional to run some penetration tests. They will find your computer system’s vulnerabilities which still need fixing. After improving and implementing the system, your security manager can thoroughly observe the IT infrastructure providing real-time monitoring.
An average IT professional cannot fill cyber security roles; most duties require a different skill set. Thus, many capable professionals opt for an online masters in cyber security. When hiring a cybersecurity team, remember to run background and credibility checks to ensure you leave the system development in safe and able hands.
Set Up a Firewall
One of the best data protection techniques is to prevent malicious links from connecting to your network. For this reason, you should set up a firewall on your system.
The firewall creates a barrier for all external networks and acts as a traffic controller; any access request that is either unrecognizable or has an unknown source is blocked before it enters the system parameters.
Most devices have a built-in hardware firewall; you just have to turn it on to improve your system security by 60% to 80%. You can also add a software firewall to improve internal security by keeping application and port traffic in check. Adding more firewall layers or using a Next Generation firewall with a multi-layered approach and intrusion prevention system can further enhance the system’s security.
Think Before Clicking
Phishing is one of the most common cyberattacks. Phishing attacks are a form of social engineering through which scammers attempt to steal user data such as login credentials and credit card numbers.
Often, scammers send innocent-looking emails which contain malicious links. These links can result in your system freezing under a ransomware attack, installing malware, or in some cases, revealing sensitive information. Sometimes, phishing attacks are more targeted; this spear phishing technique involves the scammer doing research and impersonating someone from within the organization. Spear phishing can easily trick many. To prevent spear phishing, use company-issued encrypted emails.
Remember, be vigilant and avoid clicking on links or emails from an unknown sender – a simple careless click can be fatal to your company’s future.
Use and Then Carefully Discard
The information you used a month ago might not be helpful for you now, but a scammer can still use it for extortion. Likewise, the bank notifications and account alerts overflowing your emails can give hackers enough information to put together and slide into your network. Scammers can sometimes manipulate these pieces of information through social engineering techniques to penetrate a system or steal data externally. Hence, properly disposing of any data and emails you don’t need anymore is critical.
The “use and carefully discard” practice applies to hardware too. Instead of throwing away used electronics after regular deleting procedures, consider destroying them or using certified cleaning or sanitization. The program method of sanitization can vary depending on the disk drive company. Still, the result is the same: your deleted data is completely unrecoverable and can pose no harm in the future.
Pick Your Password Carefully
24% of Americans have used “password,” “Qwerty,” and “123456” as their passwords. With effortless passcodes like these being so common, it is no surprise that 61% percent of breaches directly result from compromised or weak credentials. Choosing a good password can significantly reduce the chances of your data being stolen. Long and challenging combination passwords that do not include your personal information are the best way to go. Select a password that can withstand a brute force attack and cannot easily be guessed by the combination-constructing computer.
Remember to use the account and function-specific passwords: every login password is unique. If one social media account gets hacked, other apps will still be safe. If you run a business, ensure your employees use a different password for work-related logins than the ones they use in their personal life. Lastly, never share passwords. If you ever have to share your password with an associate, avoid sharing it through an online platform and remember to change it later.
Encrypt your Data
Even after several layers of system protection, hackers can still find a way to get their hands on your data. In this situation, you can plan one step ahead and make the data useless for them by encrypting it.
Encrypting the data converts simple text into scrambled and unreadable form. This makes data encryption ideal for information transfer as it can drastically reduce the chances of data misuse. The data can only be decrypted or turned into its usable form if you have the secret key. It ensures the data is received and used alone by the receiver it was intended for.
Finally, the encryption process is run by algorithms such as TwoFish, RSA, and Advanced Encryption Standard (AES). It ensures the whole process is automated and no data is left unsecured.
In a Nutshell
With cybercriminals preying on businesses, the internet is an unsafe place. Data can be stolen and misused easily, making it essential to make IT and data security more vigorous. You can ensure your company doesn’t have to bear the expenses and trouble of data breaches by taking these few precautionary steps mentioned above.