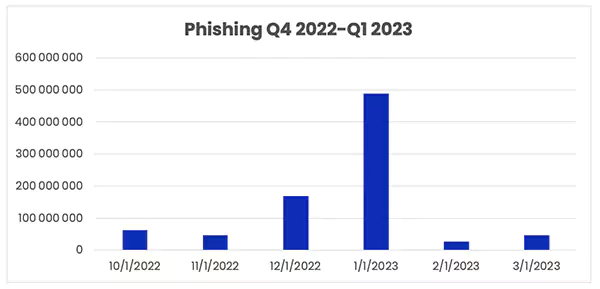
Real-Life Examples of Phishing Schemes and Lessons Learned

Key Takeaways:-
Back in 2014, a hacking group leaked information from the film studio Sony Pictures. Facebook and Google were scammed resulting in a $121 million loss collectively.In 2020 a data security breach against US DOI’s internal systems was reported by Nextgov.
Although there is very little written about small businesses that have the disadvantage of being a victim of a phishing attack, there is plenty of documentation about the larger companies that have fallen foul of cyber criminals.

This info includes how they were targeted, how much the danger cost them financially, and how they dealt with those they thought responsible – whether they were those within their own companies or the cyber criminals themselves.
Money Transfer Scams
There are plenty of real-life money transfer scams available to read about on the internet, such as the scam that involved the global giants Facebook and Google. This fraud resulted in a colossal $121 million loss collectively and was carried out over a period spanning between 2013 and 2015.
Of course, the culprit was arrested and charged. However, there are plenty of other individuals prepared to go to the same lengths who may not be looking at such large global businesses for their targets.
Personal Data Scams

Personal material scams happen at home and in the office; any data that can be used to either gain entry into business files or access confidential information is worth the effort as far as a cybercriminal is concerned. In 2020 a data security breach against US DOI’s internal systems was reported by Nextgov.
It turned out that hackers had gained access to the department’s WIFI network by using an evil twin phishing attack which enabled them to steal personal input and gave them access to other sensitive applications.
The evil twin phishing attack was only successful due to the department working outside a secure Wi-Fi network and not having all the other security measures in place.
Access to Company Data
There are various reasons why a cybercriminal will target a well-known business to gain material. It can be to sell the data on the black market or use the input to provide leverage for other malicious affairs. For instance, back in 2014, a hacking group leaked information from the film studio Sony Pictures.
This information was gained via phishing emails that mimicked Apple and targeted the top executives to gain confidential data about employees and their families, along with input relating to unreleased films.
Of course, it has since become known that their true target was to stop a certain film about the North Korean leader from being released and to actively threaten any cinemas and theatres that showed it.
Other Types of Phishing Attacks
As technology progressed, the types of cyberattacks evolved and found new ways to exploit things, in this section, we will discuss other types of cyber threats that are commonly used by scammers:
- Email Phishing – It is a social engineering attack that is used to steal data like banking information, login credentials, etc., through email, instant messages, or text messages.
- Search Engine Phishing – In this type of attack, scammers set up fraudulent websites designed to collect personal data or direct payments. These sites can show up in organic search results or as sponsored ads.
- Man-in-the-middle Attack – It involves a monitor corresponding between two unsuspecting parties. These attacks can be carried out by creating a phony public WIFI network at public places such as coffee shops, shopping malls, etc.
- Malvertising – This type of phishing utilizes digital ad software to publish otherwise normal-looking advertisements with malicious code implanted with them.
How to Guard Against Becoming a Victim
Lessons learned from all of these scenarios are that they are mainly down to human error like accepting phishing scams and not seeing them as they are, clicking on unsafe links, or working from a less-than-secure Wi-Fi network. You need to back any human security measures with technical solutions such as antiviral and firewalls from reputable companies, as well as seek help and advice from experienced experts like WatchGuard Online.
It is important to remember that it is not just the small organizations nor the large ones that are only targeted; there is, in fact, a broad range. This is because there is no end to the uses personal information can be put to, and businesses as a whole hold a large amount of confidential data on their files, including employees and customers.